Difference between revisions of "APF27 PPS"
m (→IPSec) |
(→Initializing the connection) |
||
| Line 91: | Line 91: | ||
Before creating the WiFi connection, you must load the Libertas SDIO and the MMC modules: | Before creating the WiFi connection, you must load the Libertas SDIO and the MMC modules: | ||
<pre class="apf"> | <pre class="apf"> | ||
| + | # sh /usr/local/pps/scripts/reset_wi2wi.sh | ||
| + | |||
# modprobe mxcmmc | # modprobe mxcmmc | ||
i.MX SDHC driver | i.MX SDHC driver | ||
Revision as of 11:33, 25 March 2011
Contents
Description
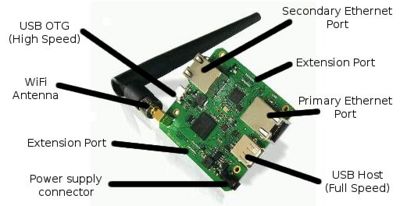
PPS is an Armadeus System's baseboard for the APF27 module. It can be used to implement and securize network applications such as routers and gateways.
Resources
Software features
There are some network applications/features that are preselected in the PPS baseboard default configuration:
- Encryption / Security
- USB Ethernet gadget support
- USB RS232 gadget support
- SMSC USB to Ethernet Adapter
- Boa Web Server
- Wireless tools (for securized WiFi with WEP encryption)
- WPA supplicant (for securized WiFi with WPA/WPA2 encryption)
| |
Note: You can also use the PPS test scripts located in /usr/local/pps/scripts on the system to test some software functionalities. |
SSH terminal
The APF27 PPS filesystem is configured to enable SSH connection from a host computer. It allows you to access a system terminal through the default Ethernet port (the one aside USB Host connector).
- The default connection informations are:
- IP address: 192.168.0.10
- Login: guest
- Password: armadeus
- Then you can connect to your system by running the following command on your host:
$ ssh guest@192.168.0.10
- For more details, refer to the SSH - Dropbear page in the Wiki.
Debug / Development interface
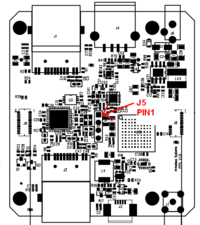
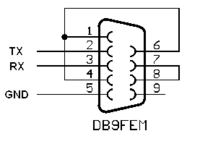
- In order to gain access to the serial port of the APF27 (U-Boot & Linux console), a small adapter cable has to be done.
A standard 2.54mm pin header connector (J5) allows accessing the TX and RX debug lines of the i.MX27. The signals are compatible with a the RS-232 standard so no level translator is required.
The pinout is described in the datasheet and summarized here:
- pin 1 (square pad): not connected
- pin 2: TX line (processor side)
- pin 3: RX line (processor side)
- pin 4: GND
- Now you have the debug access, you can install all the tools needed to control your board on your Host.
WiFi usage
On PPS, WiFi/Libertas driver usage is a little bit different than on other platforms. Here are the things to know:
Drivers setup
You have to install Libertas SDIO and MMC drivers as modules to make Wi2Wi chipset work correctly on PPS (done by default):
$ make linux26-menuconfig
Device drivers --->
[*] Network device support --->
Wireless LAN --->
[*] Wireless LAN (IEEE 802.11)
<M> Marvell 8xxx Libertas WLAN driver support
< > Marvell Livertas 8388 USB 802.11b/g cards
<M> Marvell Libertas 8385 and 8686 SDIO 802.11b/g cards
<M> MMC/SD/SDIO card support --->
*** MMC/SD/SDIO Card Drivers ***
<M> MMC block device driver
Initializing the connection
Before creating the WiFi connection, you must load the Libertas SDIO and the MMC modules:
# sh /usr/local/pps/scripts/reset_wi2wi.sh # modprobe mxcmmc i.MX SDHC driver mmc0: new SDIO card at address 0001 # modprobe libertas_sdio lib80211: common routines for IEEE802.11 drivers libertas_sdio: Libertas SDIO driver libertas_sdio: Copyright Pierre Ossman libertas_sdio mmc0:0001:1: firmware: requesting sd8686_helper.bin libertas_sdio mmc0:0001:1: firmware: requesting sd8686.bin libertas: 00:19:88:11:6b:d8, fw 9.70.3p36, cap 0x00000303 eth1 (libertas_sdio): not using net_device_ops yet libertas: PREP_CMD: command 0x00a3 failed: 2 libertas: PREP_CMD: command 0x00a3 failed: 2 libertas: eth1: Marvell WLAN 802.11 adapter
Then all informations on Libertas_driver page apply.
Shutdown WiFi interface
You have to unload the MMC driver along with the Libertas SDIO if you want to completely shutdown the WiFi interface:
# ifconfig eth1 down # rmmod mxcmmc # rmmod libertas_sdio
Reset Wi2Wi
To reset the chipset, you have to use the Wi2Wi RESET GPIO:
# source /usr/bin/gpio_helpers.sh # gpio_mode PE11 1 # gpio_set_value PE11 0 # gpio_set_value PE11 1
Test scripts
You can find test scripts in PPS' filesystem to help you to test the PPS' functionalities. They are located in the directory /usr/local/pps/scripts but you can run them from any directory.
Boa
- File
- init_boa.sh
- No argument
- Usage: init_boa.sh
- Functionality: Enable a web server with an interpreted HTML page accessible from outside the system.
USB Gadget
Ethernet Gadget
- File
- test_ether_gadget.sh
- No argument
- Usage: test_ether_gadget.sh
- Functionality: Activate an Ethernet connection interface on the system through the USB Gadget port.
- Test: Try to ping the system from your host PC on 192.168.10.1.
RS232 Gadget
- File
- test_rs232_gadget.sh
- No argument
- Usage: test_rs232_gadget.sh
- Functionality: Enable a RS232 connection interface on the system through the USB Gadget port.
- Test: Enter some datas or texts through /dev/ttyACM0 on your host PC. You should see the same datas displayed on the system.
Bridge
- File
- test_bridge.sh
- No argument
- Usage: test_bridge.sh
- Functionality: Create a bridge through two connection interfaces on the system.
SMSC95xx
- File
- test_ether_smsc95xx.sh
- No argument
- Usage: test_ether_smsc95xx.sh
- Functionality: Create an Ethernet connection interface through the Ethernet SMSC95xx port.
- Test: Try to ping the address 192.168.0.251 on your host PC.
Wifi
IWConfig (WEP)
- File
- test_wifi.sh
- No argument
- Usage: test_wifi.sh
- Functionality: Create a Wifi connection interface with IWConfig (WEP encryption).
- Test: Ping the address 192.168.0.251 on your host PC.
WPA Supplicant (WPA/WPA2)
- Files
- init_wpa.sh
- reset_wi2wi.sh
- stop_wpa.sh
- Arguments
- SSID: Wifi connection SSID
- PASSPHRASE: Wifi connection passphrase
- Usage: init_wpa.sh SSID PASSPHRASE
- Functionality: Create a Wifi connection interface with WPA Supplicant (WPA/WPA2 encryption).
- Test
- Ping the address 192.168.0.251 on your host PC.
- To unable the connection, you can run stop_wpa.sh.
- To restart WPA Supplicant, first run stop_wpa.sh then init_wpa.sh again.
OpenSSH
- File
- test_ssh_tunnel.sh
- Arguments
- USERNAME: the login of the user you want to connect on.
- HOSTADDRESS: the IP address of the host PC you want to connect on.
- VIRTUALPORT: the virtual port used to hide the encrypted port.
- TELNETPORT: the number of your Telnet port (must be same on the system and the host PC)
- Usage: test_ssh_tunnel.sh USERNAME HOSTADDRESS VIRTUALPORT TELNETPORT
- Functionality: Create a SSH connection between the system and your host PC on the Telnet port.
- Test: To test it, launch a Wireshark on the host PC to check the datas on your host IP address. The password you type and the name of the Telnet protocol must be encrypted.
IPSec
- File
- test_ipsec.sh
- Argument
- IPADDRESS: the system's IP address of the encrypted connection
- Usage: test_ipsec.sh IPADDRESS
- Functionality: Encrypt the connection between your host PC and the system.
- Test
- Before running the script, edit the file /etc/ipsec-tools.conf and put the right IP addresses for the system and your host PC.
- Launch Wireshark on your host PC on the encrypted connection's IP address.
- Run Telnet on the system toward your host PC:
telnet HOST_ADDRESS
- Your login, password and the name of the Telnet protocol must be encrypted.
Feature list
Wired communicationWireless communication |
Other
|
FPGA |